By the end of next year, the Defense Information Systems Agency wants Defense Department components to be able to buy cloud computing services through automated, Web tools. It’s a capability DISA is rolling out as part of its new role as DoD’s official “cloud broker.”
DoD’s first-ever cloud computing strategy, released one year ago, gives DISA a lead role in DoD’s migration to cloud services, and tells the agency to act as the department’s one-stop-shop for cloud services.
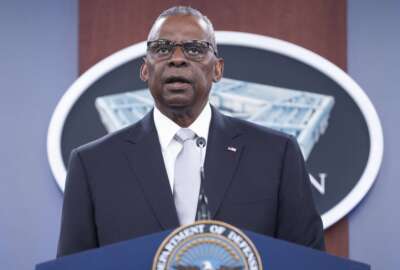
The intent, said DISA Director Lt. Gen. Ronnie Hawkins, is that military departments and agencies will select an array of options, including cloud services managed by DoD itself, other federal agencies, and private sector providers, through an automated portal.
“Right now, they’ve got to come in, we’ve got to talk to them and, in point of fact, we’re hand-jamming that information in,” he told AFCEA’s annual Cyber Symposium in Baltimore, Md. last week. “But we want to do it in a way so that all of this can be automated, and we’re working very, very feverishly to get that done. To do that, we need to make sure we have the capabilities and requirements from our providers and consumers. We’ve met with many industry partners already and we’re teaming with them on how we build the algorithms to automate this capability and put it out so that our consumers can use it.”
Hawkins said DISA hopes to have the online brokerage service at full operational capability by the third or fourth quarter of fiscal 2014. For some of the initial cloud migrations, he said DISA and the military services want to prioritize some of the websites and other services that are designed to be accessible to the public, and therefore have lower security requirements.
“They can go online, determine what they want to do, and we can send them to where they need to go,” he said. “There are a lot of public-facing applications and capabilities that we can put out there right now. We’re working with all of the services to see about putting some of those into a public cloud so that we can do this as a joint venture and we can achieve some of the requirements that we have for the JIE.”
Enterprise email to expand
The JIE is DoD’s Joint Information Environment. It’s still in the planning stages, but DoD expects to make heavy use of cloud services as part of the overall effort to collapse its networks under a common set of technical standards and a single security architecture. DISA will play a major role, given its responsibilities to maintain DOD’s global network backbone, handling security approvals and providing enterprise services for the entire military.
Hawkins said DISA already has gone a long way toward deploying its first major DoD-wide service — email. It’s now in use by most of the Army, the military’s Joint Staff and a handful of the military’s combatant commands. He said his agency now is working with the Pentagon to migrate users in the sprawling Office of the Secretary of Defense to enterprise email.
One of the next fronts in enterprise IT capabilities will be unified communications — integrating voice, video and data capabilities into a single technology infrastructure.
“Everything over IP is where we’re going. We’ve got a number of pilots underway and we’re looking at a unified capability being released out of DISA during fiscal 2015,” he said. “We want to be able to normalize our networks so that you can have collaboration over our networks, and you don’t have to have separate firewalls and networks to get business done. More importantly, we see a lot of savings in just the instruments alone, going from the hard phones that we have to softphones. We have to make sure we can get the information to our soldiers, sailors, airmen, marines and coastguardsmen wherever they happen to be. We really see [unified communications] and mobility as the disruptive technologies that we’re going to be implementing for DoD and it’s going to change the way we do business on a daily basis.”
Secure the data, not the network
And Hawkins said DoD believes removing the firewalls that prevent unified communications over IP today also will dramatically improve the department’s overall cybersecurity posture.
Another element of JIE involves creating a single security structure so that DoD’s networks aren’t walled off from one another, while at the same time reducing the number of connection points between military networks and the outside world.
“In the past, we’ve all been about protecting our networks. A firewall here, a firewall there, and firewalls within organizations including DISA,” he said. “We’ve got to remove those, and we’ve got to move toward protecting the data instead. We have to tag the data in such a way that it doesn’t matter whether you’re on a classified or unclassified network, we can move data to the right user at the right time, dependent on their credentials, their need to know and their need to have access. We want to collapse those security boundaries and reduce the attack surface we have in DoD.
“We know that also improves our ability for cyber command and control. That’s one of the things at the top of [Gen. Keith Alexander’s] list, to be able to see all the way down through the enterprise.”
RELATED STORIES:
” target=”_blank”>First elements of DoD’s Joint Information Environment come together in Europe