Best listening experience is on Chrome, Firefox or Safari. Subscribe to Federal Drive’s daily audio interviews on Apple Podcasts or PodcastOne.
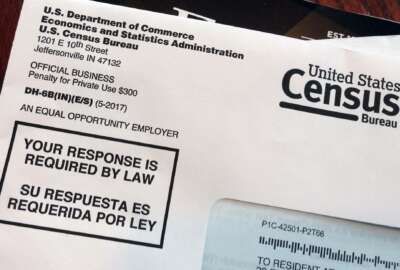
As the Census Bureau ventures into uncharted waters — rolling out the IT infrastructure allowing households to respond online to the 2020 population count — current and former cybersecurity officials want to give the American public more peace of mind.
In a letter to Commerce Secretary Wilbur Ross and acting Census Director Ron Jarmin, the former officials urged the agency to shed more light on steps it’s taking to ensure data collected from nearly every household in America will not fall into the wrong hands.
“Ultimately, the accuracy of the 2020 Census will be improved by enhancing the public’s confidence in the secure collection and safe storage of that information,” the officials wrote in July.
Joshua Geltzer, a former senior director for counterterrorism at the National Security Council under the Obama administration, who included his name on the letter, said he and his colleagues felt concerned that lawmakers were left in the dark over census preparations.
“That combination — the sense of import, and then the sense that even those on the Hill pursuing oversight on this issue weren’t getting informed about it — it struck me, it struck the others who were involved in that letter, I think, as being ripe to try and learn more. And ideally, you elicit more information and you bolster confidence,” Geltzer, now the executive director of Georgetown Law’s Institute for Constitutional Advocacy and Protection, said in an interview Monday.
Balancing data security and user experience
Earlier this year, House Oversight Committee Chairman Trey Gowdy (R-S.C.), and committee members Rep. Mark Meadows (R-N.C.) and Rep. Gerry Connolly (D-Va.), expressed frustration with the Census Bureau’s “failure to respond” to their requests for updates on 2020 preparations.
The committee had scheduled a public hearing on 2020 census IT preparations in July, but “due to scheduling conflicts,” a staffer told Federal News Radio, the hearing was rescheduled as a closed-door briefing.
Commerce Department Chief Information Officer Rod Turk, in an Aug. 31 blog post, wrote that the volume of cyber threats facing the 2020 census required an “all-hands-on-deck” approach.
“Like anything connected to the internet, Census systems, networks, and data must be properly secured against cyber threats,” Turk said. “The challenge is balancing data security and user experience while ensuring public trust. Because of this, preventing disruptions to capabilities while preparing against increasing and sophisticated threats is a never-ending effort.”
In a recent penetration test of the site that households will use to respond to the 2020 count, private-sector partners were “unsuccessful” breaking into the site.
Geltzer said these cybersecurity updates help build public confidence in the Census Bureau’s internet-driven count.
“You help the American people understand the way in which their information is being handled securely and protected. It reassures them, it increases participation in the census, which is something all of us want,” he said.
Census CIO Kevin Smith also gave an in-depth look at how the agency plans to defend against internal and external cyber threat at the agency’s quarterly program management review last month.
“I want to stress that our team has been doing everything we can to protect the data, but we are intentionally not saying everything we are doing,” Smith wrote in an Aug. 13 blog post reviewing steps his team has taken to secure the decennial count.
For example, Smith confirmed that Census would encrypt data sent through the agency’s website and from enumerators’ iPhones used when going door-to-door.
“That strikes me as reasonable reassurance — almost baseline standards these days — without of course explaining exactly what encryption protocols we use, or any way suggesting how one might, if one wanted to, try to undermine that encryption,” Geltzer said. “That’s the type of thing where you can say the standard without increasing vulnerabilities.”
Geltzer added that Smith struck the right balance in keeping the public informed about cybersecurity, but without divulging too many details.
“As former government officials, all of us who signed onto that letter are conscious of not wanting to show one’s hand, if you’re the government, in a way that aggravates any vulnerability,” he said. “That’s something that none of us would be for. But there are ways to offer reassurance at a level of generality that bolsters public confidence, but doesn’t offer any sort of vulnerability.”
Copyright
© 2024 Federal News Network. All rights reserved. This website is not intended for users located within the European Economic Area.